- Little Snitch Installed Files 2017
- Little Snitch Installed Files Download
- Little Snitch Installed Files For Mac
- Little Snitch For Pc
Little Snitch is a traditional software firewall for macOS. You can use it to monitor applications, preventing or permitting them to connect to attached networks through advanced rules. OpenSnitch is a GNU/Linux port of the Little Snitch application firewall written in Python.
The software is still in early stage of development, and alpha quality software, don’t rely on it (yet) for your computer security. However, this software can be very useful for Linux desktop users.
Sep 30, 2010 Open Little Snitch Configuration on your old iMac and choose Rules Back up Rules from the menu. Then import the resulting backup file on your new iMac and using the Revert to Backup command. Jwsd wrote:Also, do I just download the latest install file of little snitch and use my original licence key? Uninstaller of Little Snitch 4.2 do not remove its all respective files completely The software you are using to uninstall Little Snitch 4.2 is not compatible with this application. Its some files left in the hard drive or inside the resgistry so application can not be removed properly. Jan 15, 2020 1st download Little Snitch 4.5.1 with Crack Latest Version and then install it. After installing it, now check installed file location. Run its crack file from download folder. Copy keys from it and paste it in registration bar. Wait till to complete registration process. Finally, full version Little Snitch 4.5.1 with License Key is ready to use.
Installation
Little Snitch Helper is installed in /Library/Little Snitch/Little Snitch Helper.app. But I assume that it properly deinstalled, the only thing remaining is the entry you are looking at which was required to give the application access to location data. Mar 31, 2020 Little Snitch 4.5.0 Crack can be only a small parcel of applications at the menu pub, which activated tells you which apps are hoping to gain access to the internet. Once it finds an association effort, it exhibits an email providing the preference to take or refuse that accessibility and also to specify whether it’s worth forever or merely.
Little Snitch Installed Files 2017
Install required software using apt-get command:$ sudo apt-get install build-essential python-dev python-setuptools libnetfilter-queue-dev python-qt4 python-gtk2
Sample outputs:
Clone the repo:$ git clone https://github.com/evilsocket/opensnitch.git
Install it:$ cd opensnitch
$ sudo python setup.py install
Run it:$ sudo opensnitch
Sample outputs:
The Little Snitch application firewall will start working immediately and will show dialog as follows:
You can allow, deny or whitelist apps. I hope the author will continue work on this app and releases a beta and stable version for the good of GNU/Linux users. For more info visit project home page here.
ADVERTISEMENTS
Malware pushers are experimenting with a novel way to infect Mac users that runs executable files that normally execute only on Windows computers.
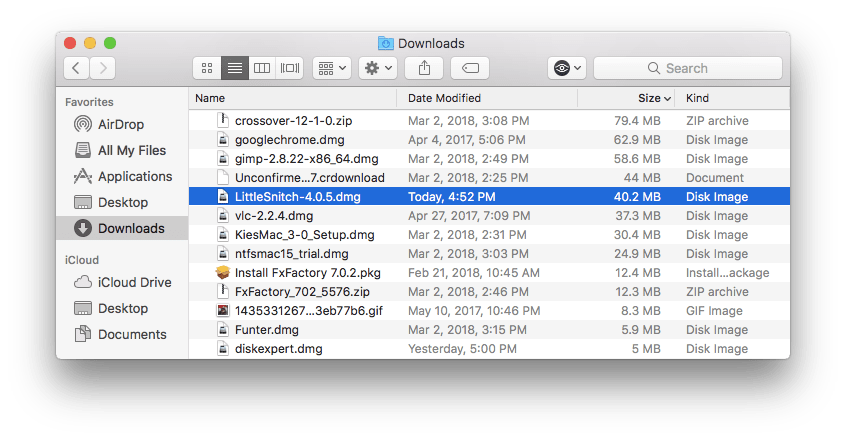
Researchers from antivirus provider Trend Micro made that discovery after analyzing an app available on a Torrent site that promised to install Little Snitch, a firewall application for macOS. Stashed inside the DMG file was an EXE file that delivered a hidden payload. The researchers suspect the routine is designed to bypass Gatekeeper, a security feature built into macOS that requires apps to be code-signed before they can be installed. EXE files don’t undergo this verification, because Gatekeeper only inspects native macOS files.
“We suspect that this specific malware can be used as an evasion technique for other attack or infection attempts to bypass some built-in safeguards such as digital certification checks, since it is an unsupported binary executable in Mac systems by design,” Trend Micro researchers Don Ladores and Luis Magisa wrote. “We think that the cybercriminals are still studying the development and opportunities from this malware bundled in apps and available in torrent sites, and therefore we will continue investigating how cybercriminals can use this information and routine.”
By default, EXE files won’t run on a Mac. The booby-trapped Little Snitch installer worked around this limitation by bundling the EXE file with a free framework known as Mono. Mono allows Windows executables to run on MacOS, Android, and a variety of other operating systems. It also provided the DLL mapping and other support required for the hidden EXE to execute and install the hidden payload. Interestingly, the researchers couldn’t get the same EXE to run on Windows.
Little Snitch Installed Files Download
The researchers wrote:
Little Snitch Installed Files For Mac
Currently, running EXE on other platforms may have a bigger impact on non-Windows systems such as MacOS. Normally, a mono framework installed in the system is required to compile or load executables and libraries. In this case, however, the bundling of the files with the said framework becomes a workaround to bypass the systems given EXE is not a recognized binary executable by MacOS’ security features. As for the native library differences between Windows and MacOS, mono framework supports DLL mapping to support Windows-only dependencies to their MacOS counterparts.
The Little Snitch installer the researchers analyzed collected a wealth of system details about the infected computer, including its unique ID, model name, and the apps installed. It then downloaded and installed various adware apps, some of which were disguised as legitimate versions of Little Snitch and Adobe’s Flash Media Player.
Little Snitch For Pc
While the Trend Micro researchers specifically mentioned Gatekeeper as one of the protections the EXE may be designed to bypass, Thomas Reed, director of Mac offerings at Malwarebytes, said definitively that there's no such bypass taking place. Patrick Wardle, a macOS security expert and chief research officer at Digita Security, agreed. They say there's no bypass because the EXE's main delivery mechanism is a standard machO binary that Gatekeeper inspects and will block if it's unsigned or has a revoked certificate.
Still, the discovery underscores the cat-and-mouse game that plays out almost endlessly between hackers and developers. As soon as developers devise a new way to protect users, hackers look for ways to get around it. When hackers are successful, developers then introduce a fix that remains in place until hackers find a new way to skirt the protection.
In 2015, macOS security expert Patrick Wardle reported a drop-dead simple way for malware to bypass Gatekeeper. The technique worked by bundling a signed executable with a non-signed executable. Apple fixed the bypass weakness after Wardle reported it. Company representatives didn’t immediately respond to an email seeking comment about the reported ability of EXE files to bypass Gatekeeper.This post was updated on 2/13/2019 at 9:19 AM to make clear the Gatekeeper bypass isn't successful.